Top Vulnerability Scanning and Penetration Testing Tool – That’s SecPoint® Penetrator™
Prevent hackers from entering and exploiting the weak spots in your servers and systems
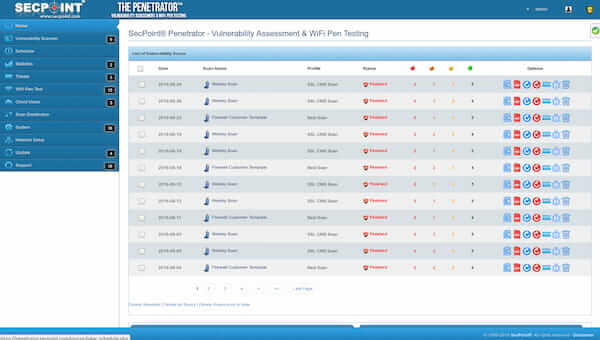


SecPoint® Penetrator™ is a vulnerability scanning and penetration testing appliance that reveals any weak spots in your systems and allows you to simulate how a hacker would exploit these vulnerabilities. It also comes pre-loaded and ready-to-go with all sorts of invaluable penetration testing features that no administrator can do without.
Apart from its ability to empower your IT teams, SecPoint® Penetrator™ also generates accurate reports which should help strengthen your security measures against online outlaws, virtual villains, cyber criminals, techno terrorists, and other nefarious elements of the Worldwide Web at large.
It’s the #1 Vulnerability Assessment and Penetration Testing (VAPT) solution which has all the data and customer location privacy and second-generation advanced AI & machine learning.
Acquire Your Key to Better Security Management
SecPoint® is trusted by thousands of security professionals. It’s considered as one of the pioneers in preventing automated hacking tools inflict damage to your infrastructure. Here are the reasons why they choose it:
Vulnerability Scanning Features
Pre-Loaded Penetration Testing Features
Scanning of Specific Ports
Flexible and Scalable
Wi-Fi Auditing
Automatic Web Crawling
CMS Vulnerabilities Scanning
Cross Site Scripting (XSS)
SQL Injection and Blind SQL Injection
Centralized Reporting and Data Storage
Multi-User Support
Scheduled Scanning & Alerts
Onboard Firewall Security
Integrated Control
Discover Vulnerabilities, Simulate Attacks, and Be One Step Ahead with These Key Features
Empower your IT and Security Teams to outsmart cybercriminals and stay one step ahead of their exploits with a fully featured VAPT tool.
Scans Any Operating System or Network Device
Expansive Distributed Penetrator™ Capabilities
Effective Launch of Real Exploits and DDoS Attacks
Identifies 108,000+ Vulnerabilities
Supports Multi-User Support for Privacy
Allows Blind SQL Injection & Web Shells
Generates Professional
Reports
See the Difference Between SecPoint® Penetrator™ Models
| Specifications |
SecPoint Penetrator 59-4-32 IPs |
SecPoint Penetrator 59-8-64 IPs |
SecPoint Penetrator 59-128-256 IPs |
SecPoint Penetrator 59-512-2048 IPs |
|---|---|---|---|---|
| Height | Small Form Factor (SFF) | 1U Rackmount | ||
| Weight |
SFF without packaging: 2.5 kg SFF with packaging: 3.5 kg 1U without packaging: 6.5 kg 1U with packaging: 8.5 kg |
1U without packaging: 6.5 kg 1U with packaging: 8.5 kg |
||
| Power Supply | 60w AC/DC 100-240V | 250w AC/DC 100-240V | ||
| Environment Temperatures |
Operating -20°C to 50°C Storage: -40°C to 70°C |
|||
| 64 Bit Platform | ||||
| SSD Included | ||||
| Network Ports | 4x 10/100/1000 Mbit | 6x 10/100/1000 Mbit | ||
| 108.000 Vulnerabilities | ||||
|
Launch Real Exploits & Denial of Service |
||||
| Allowed to Change IP Addresses | ||||
|
Distributed Vulnerabilities Scanning |
||||
|
Automated database and software updates |
||||
FAQs
Penetrator is a complete Penetration Testing, Vulnerability Scanning Suite. Portable Penetrator can scan any IP over a Wired Network for vulnerabilities. The system scans and searches for over 50,000 types of vulnerabilities literally on any IP address. Further you can Launch Real Exploits in order to check how secure your network is. Penetrator is available as an Appliance as well as a Software which runs over VMWare.
Yes, it can be easily done through the interface.
Yes, you can easily schedule a scan using it’s online interface. So the scan will initiate at your specified time. You can also instruct the system to send you an E-Mail as soon as a new vulnerability is found while scanning.
Yes, Basically it’s the same software. So every features remains the same.
Yes, some people prefer Software over an Appliance and some people prefer Appliance over a Software. When you get the appliance you just need to connect the Network cables, Plug on the system and you are done. Whereas on VMWare software you have to install, config the systems, have to get some hardware for the network cables, etc. So it’s all about what is your preference. The features, interface, etc remains the same.
Correct. That’s the reason we have designed Penetrator in such a way that it does not kill or harm the network. So it scans using failsafe procedure and is completely safe to use.
First of all it identifies, then it does a Trace Route, Check DNS, Then it does a Port Scan, then it does attacks. It does over 50,000 checks.
Yes you can easily do distributed scanning.
For example scan a system in another country.
You can also easily set centralized update point.
It means how many concurrent scans at the same time can run.
So a 8 IP license can run 8 scans at a time.
Yes, it checks more than 50.000 vulnerabilities and audits firewalls, routers, voip, windows, linux, macOS, and more.
Yes you can easily setup the schedule to run daily , weekly, monthly scans.
It means that you can launch an exploit if the target system is vulnerable.
Then you can get administrator or root access on the target system fully compromising it.
Yes you can change them as you like.
The only limitation is how many concurrent scans can run.
Specifications / System Requirements
Need to know more? Hear it straight from the experts!
We are always ready to answer your questions and tell you more about what this solution can do for your organization – you can also schedule a FREE online or on-site demo with us!